What are Cloud Managed Services?
The need for cybersecurity is in demand as many business operations are moving towards the cloud, thus highlighting the necessity for competent cloud management services. Given its various benefits, such as flexibility, scalability, and lowered expenses, alongside increasing data volumes and sharing, major cloud landscape expansion is underway. It is not unknown that the adoption, however, carries certain cybersecurity challenges, including cyber threats, ransomware attacks, and data breaches due to multi-cloud security misconfigurations. A third-party service provider of IaaS, PaaS, SaaS, DBaaS, STaaS, or user management as a service, enables such services for guarding the cloud IoT solutions against potential risks, managing servers, backing up data, monitoring, and security through anti-virus configurations, Virtual Private Networks (VPN), periodic vulnerability testing, and extensive firewall management.
When risks are at bay, businesses can easily focus on strategic decision-making and other critical growth-related aspects like software development services. These services assist organizations to implement maximally secured and monitored cloud solutions against upcoming threats and to protect their digital infrastructure and information. These build the organization’s reputation and consumer trust while enhancing its posture of cloud security and risk mitigation. The global market for managed cloud IT services was estimated to be around US $134.44 billion as of 2024 and is expected to surge and reach an approximate value of US $305.16 billion by 2030, increasing at a CAGR of 14.7% during this forecast period. In this blog, we will discuss how these managed cybersecurity services enable reinforcement of data protection against ever-evolving cloud risks.
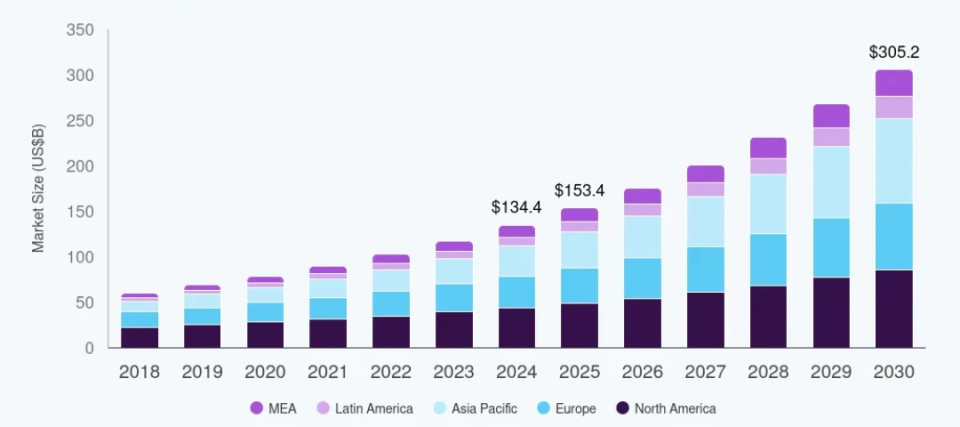
Source: Grand View Research
Growing market size of cloud managed services during the forecast period 2018 to 2030
Key Cybersecurity Benefits of Managed IT Services
In this section, we will discuss the various advantages that businesses can benefit from implementing managed services for cloud computing over public, private, hybrid, and multi-cloud platforms.
Perpetual Monitoring
These services provide round-the-clock monitoring, identification, and addressal of potential cyber threats over cloud-based infrastructure in real-time. This proactive patching approach increases accuracy of cloud-based ERP system, etc., and reduces the occurrence of large-scale breaches by tackling the probable sources. Managed cloud IT services take into consideration simplified administration, container security, Kubernetes Security Posture Management (KSPM), runtime cloud virtual machine, Cloud Security Posture Management (CSPM), Application Security Posture Management (ASPM), Data Security Posture Management (DSPM), etc.
Threat Prevention
Managed cloud services effectively prevent threats by deploying muti-factor authentication (MFA), intrusion detection systems, and firewalls. This helps in handling, containing, and reducing the implications of security breaches in a timely manner, thus acting as a resilient threat-hunting defense framework along operational margins.
Governance Services
It is compulsory to remain multi-cloud compliant with industrial regulatory standards, such as GDPR, PCI-DSS, NIST, ISO 27001, SOC 2, HIPAA, etc., especially in the finance, healthcare industries, and even in cloud-based manufacturing execution system. A managed cloud services provider (CSP) supports the same during the implementation of cloud migration services by conducting periodic compliance and regulatory audits, data loss prevention (DLP), and adopting necessary security frameworks alongside overseeing the organization’s security reporting, monitoring, and automation.
Risk Mitigation
These services utilize advanced methods of sensitive data encryption at rest and during transit to avoid unauthorized access and tamper-proof infrastructure. They execute multi-layered network security and segmentation, Distributed Denial of Service (DDoS) mitigation, rapid disaster recovery, and data backup measures in check to refrain from losing critical information. With their assistance in incident response planning and risk remediation, businesses can function continuously even during an attack or breach resulting in data loss without enduring unnecessary maintenance expenses. Cloud Infrastructure Entitlement Management (CIEM) tools, unified security management platforms, Cloud Access Security Broker (CASB) tools for cloud application modernization, etc., are often considered in such cases, as these integrate continuous threat monitoring across all cloud providers, maintains visibility and consistent policies.
Identity & Access Management
Cloud resources stay protected at all times against data breaches through identity management and access control ensured by managed cloud IT services. They ensure that only the personnel who are authorized to access sensitive data like Public Health Information (PHI) can do so through IAM protocols to prevent insider threats. They also utilize MFA and role-based access control (RBAC) measures to reduce risks and unauthorized access.
Flexible Security
Managed cloud services provide scalable cybersecurity solutions that are aligned with the growing needs of the client organization and reduce the risk of vendor lock-in. This includes deploying security measures during the addition of new users, cloud-based expansion of IT infrastructure, or integration of new applications. With the help of these services, businesses need not additionally hire cybersecurity, secure software engineering, or secure cloud infrastructure experts while scaling their operations.
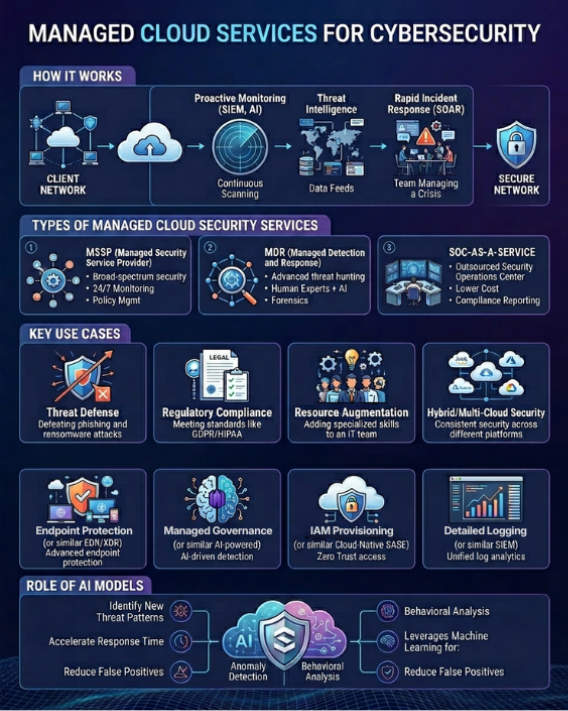
Various use cases and types of secure cloud managed services
Best Cybersecurity Practices for Cloud Managed Services
Cybersecurity over cloud-based platforms can be kept at pace through dynamic security-first cloud strategies so that the visibility requirements of the IT department always stay at par with data protection, control, and system safety. Some of the common practices followed by cloud-based cybersecurity management services are given below.
1. Protection Policies: Every business stores and protects the data that is necessary for its various operations, solution development, and projects. Such information should be categorized and guarded against unauthorized access by putting data protection policies in place. Resources working on managed cloud-based platforms can focus on crucial business or IT activities as the attack surface of critical data is significantly reduced through robust cybersecurity measures. A managed cloud services provider can offer Cloud Workload Protection Platform (CWPP), Cloud Native Application Protection Platform (CNAPP), AI-powered Endpoint Protection Platform (EPP), Endpoint Detection and Response (EDR), Extended Detection and Response (XDR), Security Orchestration, Automation, and Response (SOAR), Cloud Detection and Response (CDR), Infrastructure as a Code (IaC) Security, etc.
2. Personalized Keys: Advanced hackers can extract and exploit even the most difficult password and user ID combinations through spyware. It is of utmost importance to use secure encryption key lifecycle management by personalizing keys with MFA for data encryption and agentless vulnerability detection in lieu of single-factor authentication. This is one of the major benefits of managed IT services that helps to protect the system, such as cloud-based attendance system, reduce Active Directory (AD) risks and lateral movement, avoid breaches through login credential misuse and other malicious orchestrations.
3. Data Sharing: Based on Zero Trust and IAM strategies, sharing sensitive data can be limited to certain people who require, check, or utilize the data on a continuous or timely basis. Managed cloud security practices need to be adhered to, where unnecessarily sending and granting access of data by multiple users to people, such as clients, stakeholders, investors, remote workers, and other external guests is avoided. Making sure of this provides protection against zero-day exploits, ransomware, and phishing attacks on the extended Berkeley Packet Filter (eBPF) architecture.
4. Unmanaged Devices: Post usage of data, managed cloud IT services can prevent data mistreatment in unmanaged devices. They make sure that only secured and required devices stay connected over the network and utilize sensitive data, and no unintended recipients get hold of it. This practice is an additional layer of protection apart from data encryption in the cloud against firewall and web filter breaches.
5. Periodic Testing: Another best practice considered by these managed services is conducting routine tests and scans of the cybersecurity measures or systems for malware, Trojans, etc., such as Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), penetration, functionality, vulnerability testing, etc. As and when the critical gaps are revealed, they need to be addressed immediately. This can be done through necessary adjustments in the system or by putting additional cybersecurity measures, such as DevSecOps-based IaC provisioning, secret scans, etc., in place.
6. Resource Training: Rash errors made by employees leave a blind spot or vulnerable access point for expensive data breaches, which may pose disastrous issues in the managed cloud setup. Resources involved in IT, cloud, cybersecurity, and necessary projects involving generative AI in cybersecurity should be trained in key access management and explained about common security practices to eliminate potential risks.
Build Your Governance Framework with KritiKal
KritiKal Solutions has partnered with various managed cloud service providers, such as Amazon Web Services (AWS), Microsoft Azure Cloud, etc., to offer their platform powered with advanced cybersecurity measures. Our IT services and solutions are backed with cloud security under an effective shared responsibility model between the provider and the client organization. We ensure that the best practices are observed during login and role-based access control measures. We are transparent to our customers about sensitive data storage in ransomware-resistant storage systems like AWS S3, Google Cloud, etc. We assure clarity on data lake centralization, measures taken for its security, how raw data is transformed into actionable insights, analytics delivery and logging, critical alerts and notifications, and other potential privacy concerns.
We understand that cybersecurity over managed cloud services is the need of the hour, given the incessant threats amongst businesses and their data. Therefore, we ensure the complete cycle of cloud security to our clients through scalable solution development, enhanced threat monitoring, prevention and detection, data encryption through MFA and IAM, and checks for compliance with industrial regulatory standards for business continuity (BC) and data retention (DR). KritiKal is armed with the required tools for compliance reports, EKS, Kubernetes cluster visualization graphs, etc., to safeguard critical organizational assets within a dynamic and risky environment. Please get in touch with us at sales@kritikalsolutions.com to learn more about our cybersecure cloud and software-based solutions, products, platforms, services and realize your business requirements.
Rajat Goyal currently works as a Senior Software Engineer at KritiKal Solutions. He has over a decade of experience in building and agile delivery of enterprise software and medical-grade Windows and backend applications using .NET, C#, WPF (MVVM), ASP.NET Core, Web API, SQL Server, and cloud platforms. He is proficiently skilled in modernizing legacy systems, improving performance, and reliability in collaboration with KritiKal’s global product, QA, and engineering teams.



 Global
Global  United States
United States 
