What is Secure Software Engineering?
The rise and integration of consumer IoT devices into the fabric of modern life have revolutionized our interaction with technology, from vehicles, voice assistants, wearable trackers to smart homes. Although increased connectivity introduces a wider attack surface for cyberthreats across consumer electronics. Over the years, threats around software have evolved, which calls for advancements in methods of building software. Developers that provide software development services and users today face the risks of high bot traffic, exploitations in the supply chain, remote or virtual jobs, attacks driven by AI, and vulnerable global ecosystems powered by the cloud. Higher risks demand enhanced security built in right from the first line of code rather than end integration.
Given such conditions, secure practices put forward through IoT consulting services play the frontline role and need to be imbibed in the muscle memory while writing APIs, during production, and even during bug fixing. Securing consumer IoT software during the development cycle has emerged as an important framework to address risks related to privacy invasions and safety. It ensures that all security considerations are systematically integrated in every phase, right from conceptualization, design, development, and deployment to maintenance. This proactive approach minimizes costs that would have been expended on fixing vulnerabilities at later stages. The current global market for cybersecurity and secure software engineering services is estimated to be around US $188.66 billion as of 2026 and is expected to surge and reach an approximate value of US $310.35 billion by 2034, increasing at a CAGR of 6.42% during this forecast period. Let us now go through the importance of the same in securing the development lifecycle further in this blog.
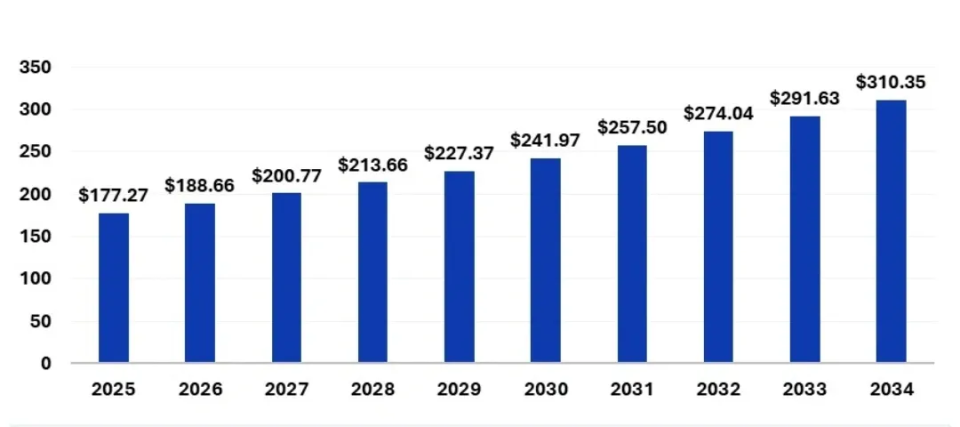
Source: Precedence Research
Growing market size of security in software development during the forecast period 2025 to 2034
Key Stages of Secure Application Development
Secure strategies are embedded in every phase of the process to ensure the security of the product in its final or production stage. Given below is a multi-stage approach for implementing a secure development lifecycle for consumer IoT software so that it can withstand the evolving threat landscape.
Requirement Collation
Developers gather requirements and define security objectives that are necessary for the product to meet, such as medical devices that deal with sensitive health metrics and user location. Potential threats are identified, and goals related to availability, confidentiality, and integrity are set using a comprehensive risk assessment while delivering web application development services. This may determine objectives like encryption of sensitive data during transit and rest, limiting authorized access, response to attack, and maintaining functionality of the device during the same. They need to consider vulnerabilities in device communications with Wi-Fi, Bluetooth, and cellular networks during data storage and transmission. Moreover, the team needs to consider legal regulations and standards like GDPR, CCPA, etc., and check for device compliance to avoid penalties.
Architectural Design
The interaction between the product’s components is determined through a robust blueprint, threat modeling, and security control implementation plan. Models like STRIDE and DREAD can be used, where the former evaluates potential weak points, and the latter provides an understanding of prioritized risks. STRIDE categorizes threats as spoofing, tampering, repudiation, information disclosure, denial of service, and elevation of privilege. Here, DREAD ranks threats as per their discoverability, reproducibility, exploration, affected users, and damage potential. A comprehensive security strategy will also involve considerations such as theft, device cloning, unauthorized access, etc.
Common design security controls integrated for security in software development are authentication (MFA), authorization (password entry for new devices), configuration management (metadata, console access, config data), encryption (AES 256), Personally Identifiable Information (PII), exception and session management, auditing and logging for traceability, communication security, high load handling, Spring Security modules, and utilization of industry standard tools. Other than these, certain principles like least privilege (minimum access to each component), defense-in-depth (layered security), and fail-secure mechanisms minimize exploitation.
Implementation
As the code is developed in this phase, it is made sure that the product design adheres to secure practices and minimizes risk to codebase vulnerabilities. Consumer electronics devices running on IoT without Gen AI in cybersecurity have limited resources and they may expose user data that is not secured. To prevent remote attackers from controlling devices, practices, such as command or data input validation, error message handling mechanisms, and techniques to avoid insecure or outdated functions, and libraries (MD5, SHA-1) are kept in place. Cryptographic libraries, automated security tools, such as static code analysis and vulnerability scanners that identify insecure implementation, memory leaks, buffer overflows, etc., should be utilized.
Testing
Post implementation, rigorous penetration testing, vulnerability assessment, and functional testing are conducted to identify areas that attackers could exploit to breach the system. This involves mimicking malicious agents, reverse engineering, debugging, binary code extraction and analysis, endpoint (sensors, nodes) and ecosystem bypass tests, DAST to secure APIs, mobile, web, or device application through mobile app development services, and Continuous Integration (CI pipeline) security tests against new code.
Maintenance
Devices need to remain secure over the entire secure software development lifecycle and further through continuous monitoring (activity logging, suspicious behavior detection, intrusion detection system), regular updates, legacy app modernization, and patching. Alongside application development and maintenance, a well-defined and rapid incident response plan to mitigate breaches, send notifications to affected users, recall, security audits, and update firmware and devices that are compromised must be put in place.
Best Secure Development Practices in Software Engineering
In this section, we will walk through the best practices of developing software as per a globally recognized baseline for related engineering known as the Software Engineering Body of Knowledge (SWEBOK). This framework forms consistent norms and defines widely accepted knowledge areas for this discipline. Not only does this assist in standardizing the engineering field but also clarifies its relative scope with other fields, such as computer vision and others. Let’s dive into some of the generally known best practices.
Secure Baseline Code
Developers need to keep in mind to write secure code by default as the baseline because a weaker foundation leads to cracks in firewalls and patches. Language-specific coding standards that are secure in nature, such as Python, Java, C, C++, etc., need to be adhered to as they follow required guidelines, including SEI CERT. These practices are tested against buffer overflows, SQL injection attacks, and race conditions. To enhance this further, secure code tools, such as CodeQL, SonarQube, etc., can be used alongside readable and maintainable versions of code that are easy to refactor or debug.
Secure Libraries
Third-party packages or software like cloud-based ERP system carry the risk of causing supply chain attacks, and therefore using secure development practices for open-source libraries and third-party code becomes a necessity. They should seldom be treated as plug-and-play software and manifested as a Software Bill of Materials (SBOM) for the codebase. The SBOM must be maintained for every release, as it highlights compromised libraries. All dependencies need to be scanned regularly for vulnerabilities using tools, such as Snyk, OWASP Dependency Check, Renovate, Dependabot, etc. This assures security right from the time vulnerabilities start emerging and not while pushing the software to production. Checksum-validated, signed, and lock file-checked packages must be used during builds.
Secure Design
Defense-in-depth can be implemented via architectural design, which can be secured by ensuring that a breach in one data layer does not affect the functioning of the entire application. This is done by using architectures that isolate components as per usage, logic, and data layers. Low access privilege principles must be applied across services, APIs, and users. Especially during design and development of wearables, teams need to secure inter-service communications across microservice-heavy applications by using mutual TLS (mTLS) for traffic encryption, schema validation, and service authentication.
Secure Testing
The code review checklist should contain vulnerability, syntax, logical testing, bug fixing, and peer code checks as part of the regimen. Apart from unit testing, thorough checks for input sanitization, broken access controls, and suspicious patterns must be conducted. Test cases focusing on security login flows, input validation, and permission boundaries must be added. Test coverage around critical functions must be tracked, and a secure test suite can be deployed to guard against the application.
Secure Lifecycle
Application security practices must be embedded right from the time when the first ticket is generated and not in the last sprint. Security must be built in every phase through adoption of a secure Software Development Lifecycle (SDLC) starting from planning, designing, and testing, till deployment. The development team can make use of threat modeling tools and frameworks, such as STRIDE, LINDDUN, etc., to pinpoint vulnerable areas. In the case of agile and scrum methodologies, security risks need to be logged, prioritized, and fixed by embedding risk analysis techniques into project planning. All features of the software must be analyzed and tested through technical and ethical aspects or strategies.
Secure Scanning
Developers can automate dynamic, static, and dependency scanning and integrate them into CI/CD pipelines, such as pull requests and builds. Issues in the code can be highlighted using Static Application Security Testing (SAST), the behavior of the app in a real environment can be tested using Dynamic Application Security Testing (DAST), and vulnerabilities in dependency can be tested using Software Composition Analysis (SCA). Fuzz testing critical components is a must-have for handling sensitive data, such as payments, authentication workflows, and health-related information.
Application Firewalls
API gateways and Web Application Firewalls (WAFs) are necessary measures to be put in front of service platforms or software prior to access. This helps to determine and control endpoints, access frequency, and locations. Furthermore, it can be further utilized to set geo-restrictions for local traffic instead of global exposure, and to set rate limits to block abuse and brute-force attempts. WAF acts as an intelligent filter to highlight known attack patterns, such as XSS, SQL injection, and payloads, prior to reaching the application or automotive IT solutions. Common cloud and non-native solution providers ensure a combination of managed WAFs and gateways to correlate with behavioral risks across cloud IoT solutions and absorb noise.
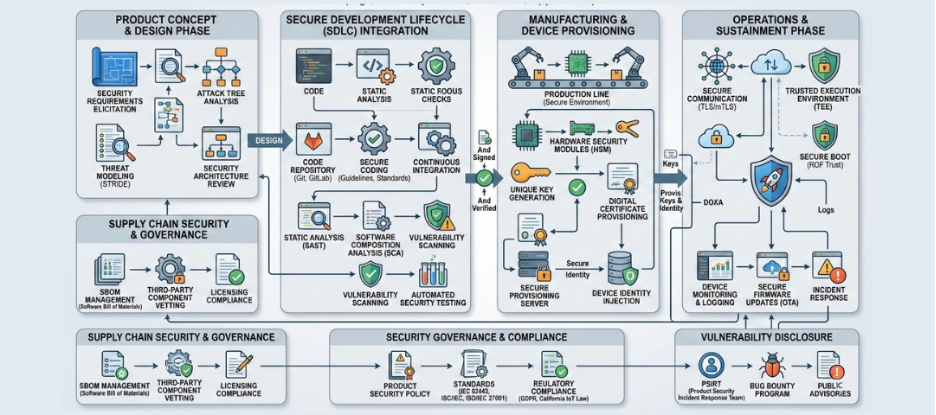
High-level architecture diagram of secure application development in consumer electronics
A Dive into KritiKal’s Secure Software Engineering
Hackers look for any vulnerability present in the interconnected network of consumer IoT devices that keep increasing day-by-day. Expanding threats create opportunities to maliciously access personal data and gain remote control of devices, leading to disrupted functionality. Developers need to embed security throughout the product or SDLC to reduce DDoS attacks on IoT devices and support compliance with standards, including ETSI EN 305 645 and UK PSTI Act. KritiKal plays a critical role in validating this process and ensuring that the devices adhere to industrial requirements through its cybersecurity management services.
We mitigate risks through thorough vulnerability assessments, compliance and certification checks, and penetration testing so that organizations can market their devices as secure and compliant. Our secure software development for the baseline for risk management, as we make room for continuous improvement and consistency in our practices while building resilient products. Please get in touch with us at sales@kritikalsolutions.com to know more about our software-based products, platforms, services, and realize your business requirements.

Bonkila Siranji currently works as a Senior Quality Engineer at KritiKal Solutions. He has over 8 years of experience working in quality assurance and handling core tools in various stream SQS, QMS, and COS. He is proficiently skilled in PPAP documentation, supplier rating, supplier, IATF, and internal audits, selection, incoming and joint inspection, material testing, quality control, SPC, MSA, Minitab, CSR, customer complaint handling, and more. With his ability to work efficiently in teams, software development, and testing, he has assisted KritiKal in delivering various projects to some major clients.



 Global
Global  United States
United States 
